Recon
What we’ll be going over in this post is external recon of the game. What I mean by external recon is just getting and overview of how the game is working without going in detail and finding entry points for exploiting.
In the Previous Post
We set up the game server and game client for both windows and linux in the previous post. One error that you might face which I faced was libssl and libcrypto was missing the game currently uses an older version of this library and I had to install it separately. link
Libraries
Lets start first by looking the dynamic libraries linked with the game binary through the ld command. 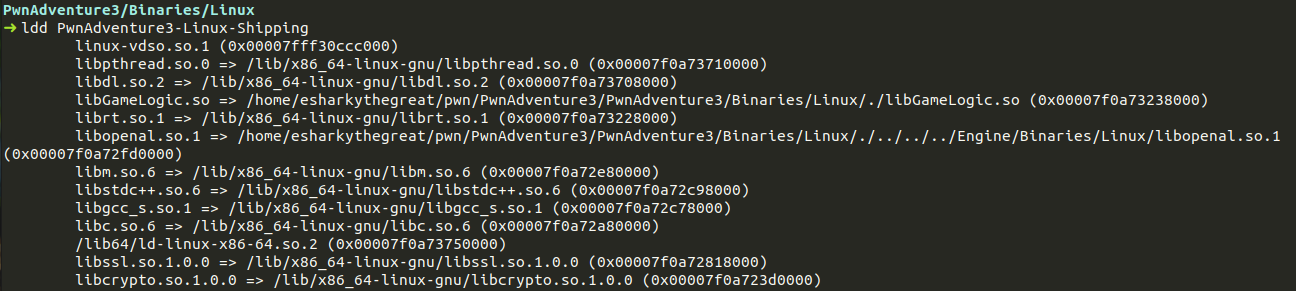 We see many common libraries which are being used. There is
We see many common libraries which are being used. There is libpthread which is used for threading. There is a custom libGameLogic library which might be useful. Using the file command on libGameLogic we see - 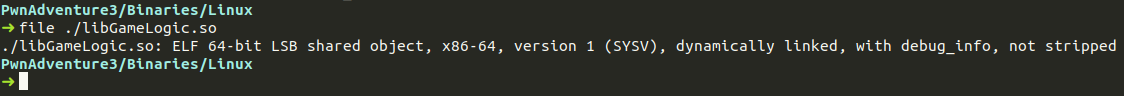 The file has debug information which makes our life a lot easier. Looking at the other libraries we see
The file has debug information which makes our life a lot easier. Looking at the other libraries we see libcrypto and libssl which might be used for encryption and TLS.
Process Overview
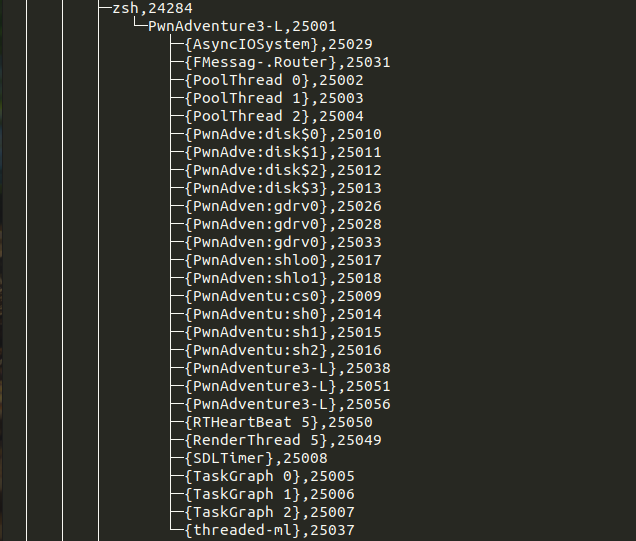
Let’s look at the process in Linux. Each process has a pid (process id). Lets see the process in pstree to see its child process and threads.
Here we see all of the threads and their pids as well all of these components must be handling some sort of functionality.
/proc/pid
The /proc is a a special directory which contains information about running processes. First we’ll grab the pid through the command -
1
ps aux | grep -i pwn
Then change the directory to /proc/pid you’ll see something like this in the directory. 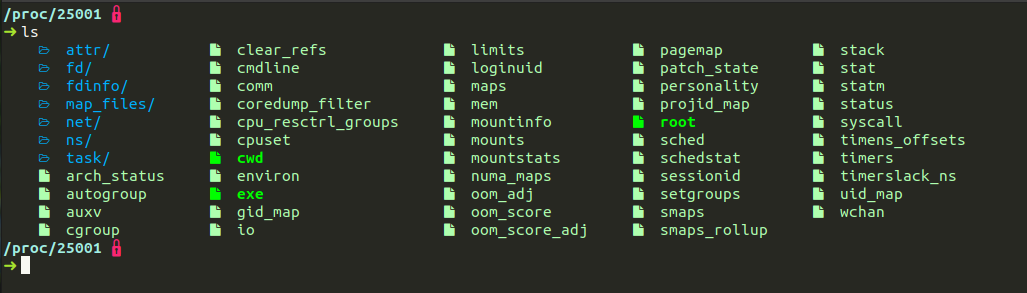 Here the files represent different information about the process. E.g
Here the files represent different information about the process. E.g cmdlineshows the cmdline arguments for running the process, maps show the virtual memory mapping of different libraries,stack,heap etc,the fd folder has info about the open file descriptors,environ has information about the environment variables. 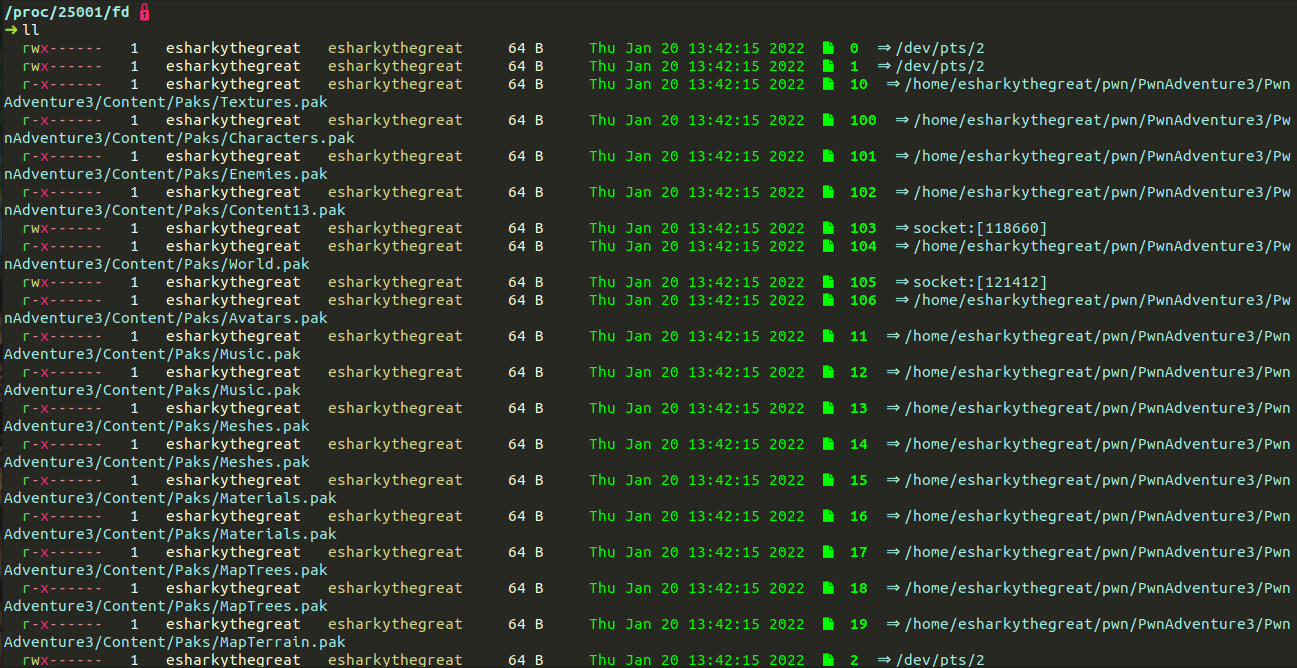 Upon inspecting the fd directory we see that there are standard file descriptors open like
Upon inspecting the fd directory we see that there are standard file descriptors open like STDIN,STDOUT,STDERR etc and also file descriptors for packed textures and models.
Network
Lets check the network side of things with the command -
1
netstat -ac | grep "pwn"
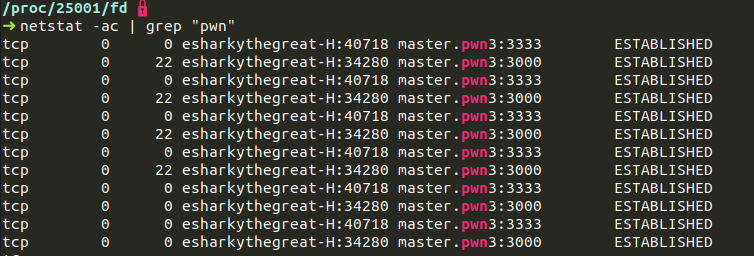 We see that there are 2 repeating connections to
We see that there are 2 repeating connections to master.pwn3:3333 and master.pwn3:3000 where the second connection is essentially to game.pwn3:3000 as its connecting to the game server and thats the hostname we gave it.
Master Server
Lets see the packets sent to the master server when the game starts. So we’ll check the packets sent to port 3333 on wireshark. 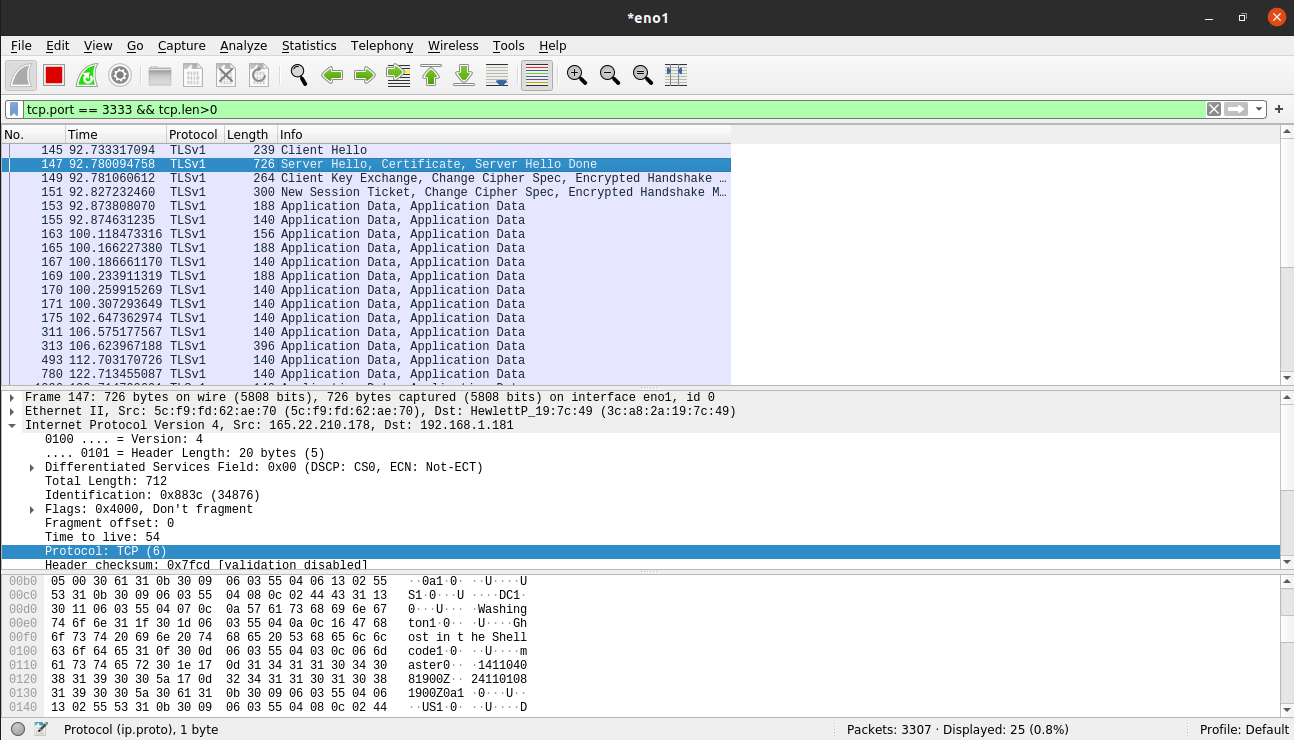 We see TLS as the protocol which must have been used for the certificate for secure communication between the master server and our client. We see strings like ghostintheshellcode which is the name of the organizer.
We see TLS as the protocol which must have been used for the certificate for secure communication between the master server and our client. We see strings like ghostintheshellcode which is the name of the organizer.
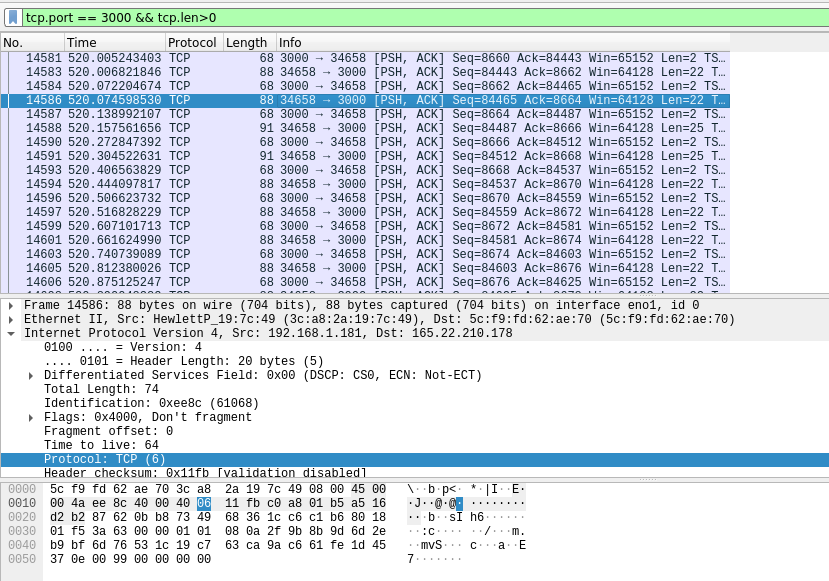
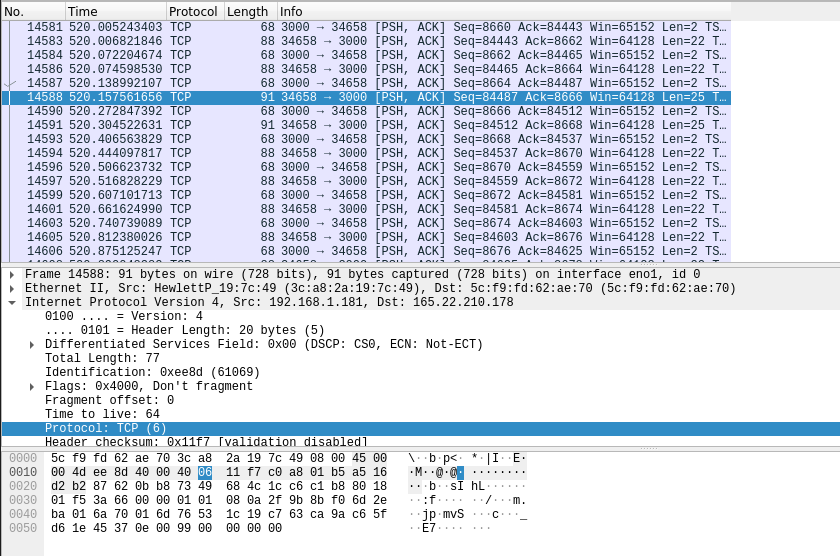
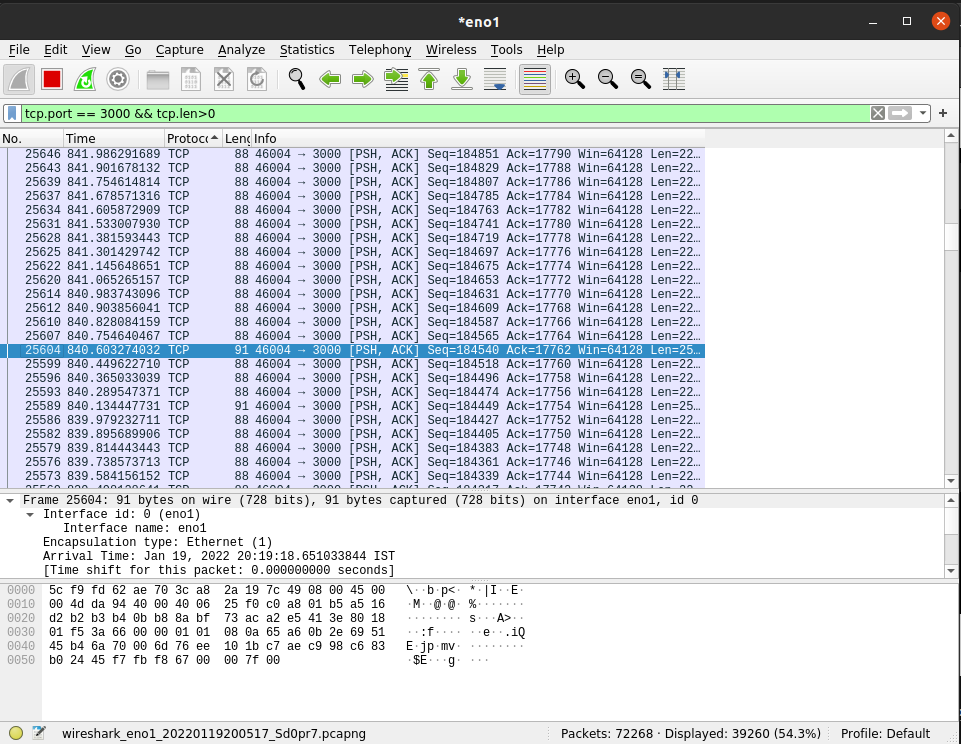
Game Server
Lets see the packets sent to the game server on port 3000 for me. We constantly see packets being exchanged between the server. There are 2 things to see.
First, When we move we see a special string mv in the packets.
Second, When we jump we see a special string jmp in the packets.